The New Map of Tiered Internet Access in Iran
From White Lines to Internet Pro: Reselling Blacklist Censored Internet to Authenticated Users

With the end of the war between the United States and Israel and the Islamic Republic of Iran in April 2026, pressure to restore an internet service that had been completely cut off pushed the Islamic Republic to implement the “Internet Pro” model of tiered internet access. In this model, internet access is no longer defined as a public and equal service, or even at minimum as a service provided over the National Information Network, NIN. Instead, access is distributed according to user class, identity verification, service commitments, professional or institutional affiliation, and the level of security trust assigned to the user. Under this model, academics, journalists, traders, businesses, and even “ordinary users” each receive a different level of access. Yet the common feature across all these categories is the transformation of the internet into a conditional privilege that can be traced and disconnected.

In other words, what has happened to internet provision in Iran after the war is not merely a continuation of previous filtering. It is a shift from blacklist based censored internet to an internet model based on whitelisting, identity verification, and session control. Evidence shows that censorship in Iran has moved from “filtering websites” to “controlling routes and sessions.” The central issue is no longer only whether a domain is blocked, but which user, from which network, under which identity, and through which path is allowed to connect. In fact, user authentication is the core of this access model.
RazNet’s previous investigations on this issue:
- Iran’s New Internet Censorship and Digital Surveillance Architecture
- How Iran’s National Information Network Works
- The Policy Architecture and Institutional Mapping of Citizen Surveillance and Espionage in the Islamic Republic of Iran
Over the past month, official reactions to “Internet Pro” have shown that even within the Islamic Republic’s governance structure, there is no unified narrative about the plan. On one hand, the government spokesperson said Internet Pro had been approved by the Supreme National Security Council to preserve business connectivity in crisis conditions. On the other hand, a deputy minister of ICT said Internet Pro is not a “development tool” or a “special privilege,” but an emergency solution whose framework is determined outside the ministry and at the level of security decision making. At the same time, the judiciary entered the case after reports of “corruption and discrimination” in the allocation of Internet Pro. Head of Judiciary, Gholamhossein Mohseni Ejei, who is himself a member of the Supreme Council of the Internet, ordered the prosecutor general to investigate, and the General Inspection Organization announced that the CEO of Mobile Communication Company of Iran, MCI, had been summoned to explain Internet Pro.
In this chaotic environment, Irancell also responded to reports that the “white internet” access of some journalists had been cut off, saying that operators have no role in bandwidth monitoring, setting access levels, or applying filtering, and that they are merely internet distributors. Taken together, these positions show that Internet Pro is not a transparent and publicly declared policy. It is instead a product shaped between security institutions, the government, operators, the judiciary, and public pressure. By examining the types of access available to Internet Pro users, researchers have identified several different categories of Internet Pro, including FilterWatch and Mamlekateh (A News Telegram Persona).
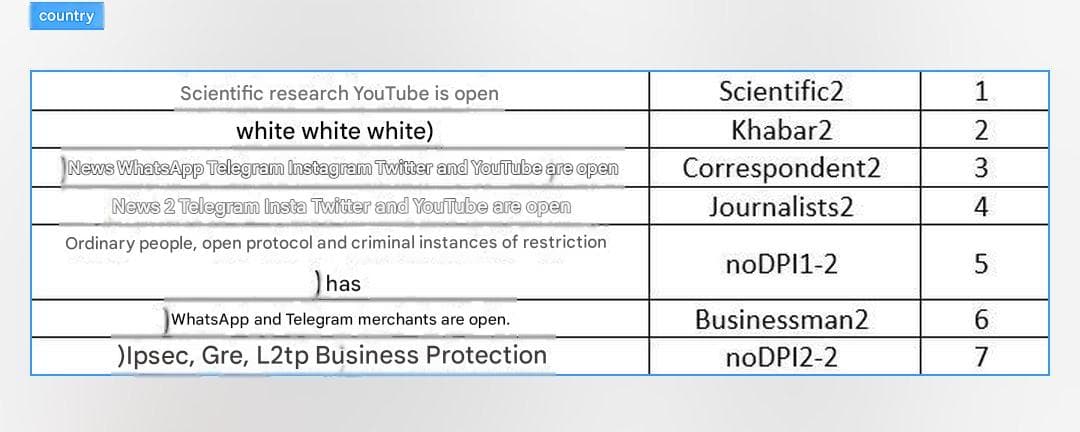
Below, we examine the different dimensions of these unequal forms of access. Among them, however, what has been described as “Internet Pro for ordinary users,” row number 5, contains evidence suggesting that internet access will no longer return to the state that existed before the protests of January 7 and January 9, 2026. We examine that issue below. But first, we look at what capabilities have been opened on the National Information Network for each of these categories.
YouTube for Academics: A Scientific Cover for Privileged Access
For the first category in the table, namely Scientific2 or “scientific research,” its traceable history goes back to the discussion of “special access for academics” and later “tiered internet for professors, researchers, and scientific centers.” In the latest wave, the Ministry of Science, Research, and Technology said that access to the internet for academics would begin “with university professors” and that “other researchers” would then be added to the list. Some reports added that in the first phase, universities professors would receive text messages to register for this access.
The history of this category is not limited to April 2026. In November 2025, reports said YouTube had been unblocked for University of Tehran students through university and dormitory internet. The University of Tehran said the purpose was “access to the latest educational resources in the world,” but the Ministry of ICT and the Communications Regulatory Authority said no resolution or official directive had been issued to provide special internet to educational centers. Earlier, in January 2025, the minister of science had spoken of efforts to unblock YouTube for students and professors, although the Ministry of ICT denied cooperation in implementing a tiered internet.
Therefore, the “scientific research” category can be understood as one of the oldest and most defensible narrative covers for tiered internet access: access to scientific and educational resources on the surface, but in practice part of an architecture of privileged and list based access in the Islamic Republic’s network.
Internet for Journalists: From White Lines to Insider and Outsider Segmentation
The publicly documented history of “internet for journalists” goes back at least to April 2018, when, after Telegram was banned in Iran, the press deputy of the Ministry of Culture and Islamic Guidance announced that, following a request by that office and follow up by the Ministry of ICT, the Committee to Determine Instances of Criminal Content (Filtering Committee) had approved “unfiltered internet” for 100 journalists. The same announcement stated that this access would be for “journalists approved by the Ministry of Culture and Islamic Guidance,” and that applicants had to submit their civil registration details, media outlet name, and mobile number for identity verification and confirmation of professional activity.
A few months later, Mohammad Javad Azari Jahromi, then Minister of ICT, said that deciding which journalist could receive unfiltered internet was not the responsibility of the Ministry of ICT and that “the responsible authority is the Ministry of Culture and Islamic Guidance.” At the same time, he acknowledged that the criticism of discrimination was valid and said that if the Ministry of Culture provided a list, the Ministry of ICT would not impose any limit on the number. From the beginning, then, “internet for journalists” was not defined as a public right to free access, but as access based on lists, identity verification, institutional approval, and administrative selection.
In the recent table, the existence of three separate categories under the titles Khabar2, Correspondent2, and Journalists2 is a more significant sign of the same list based logic. The second category, “white,” appears to go beyond the ordinary journalist category and resembles a profile fully exempt from restrictions. Such a level of access is more consistent with the concept of “white lines (SIM)” for government officials, senior regime figures, individuals close to the state, and propaganda actors than with professional journalistic needs.
The next two rows also show that even within the broad label of “journalist,” access is not uniform. One group has access to WhatsApp, Telegram, Instagram, Twitter, and YouTube, while the other apparently does not have WhatsApp. This difference may indicate a distinction between trusted journalists, semi approved journalists, and less trusted media users. It is the same structure in which the government first takes away the public right to access and then returns a selective and controllable version of that same right to chosen groups.
Traders and Businesses: Economic Internet Under Security Oversight
For the “traders” row, public evidence is almost direct. The head of the Industries and Mines Committee in parliament, has said that the “Internet Pro” plan is being implemented with the approval of the secretariat of the Supreme National Security Council for “business continuity.” In the first phase, access has been provided through the Chamber of Commerce for holders of commercial cards. He also said that in the next phase, organizations and agencies related to production, industry, and commerce would receive access, and that identity verification for smaller production units is also under way.
The Businessman2 row points to a layer that is approved through commercial cards, the Chamber of Commerce, guilds, or agencies related to trade and production. The important point is that member of parliament explicitly said that the scope or limits of access to the international internet are determined by security institutions, headed by the Supreme National Security Council. This means that even when this service is presented in the language of “supporting trade,” institutionally it is defined within a security and list based framework. Domestic newspapers have written that after businesses met with a representative of the Supreme National Security Council about the losses caused by the internet shutdown, the then secretary of the SNSC ordered that a solution be designed to prevent harm to businesses during internet outages. A committee made up of the National Center for the Cyberspace and the Ministry of ICT was then tasked with designing this model.

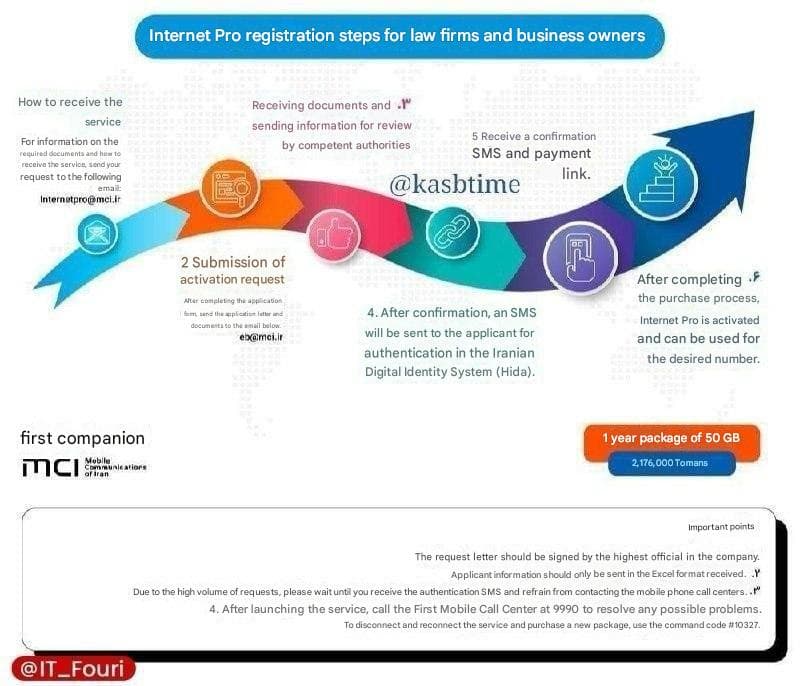
At the time, it was claimed that “Internet Pro” could only be requested by legal entities, that individual users could not buy it directly, that activation would take place on the users’ existing SIM cards, that the organization would have to submit an official service commitment, and that each user would also have to sign a separate commitment to comply with regulations. It was also said that even within an organization, not all employees would be included, and that only a limited number of people would receive access based on the size and type of the organization’s activity. This shows that the “business support” category is probably not intended for the entire community of freelancers or startups in a general sense. Rather, it is designed for authenticated, introduced, and traceable users inside companies, organizations, production units, registered startups, and internet dependent businesses.
But the phrase listed in front of the “business support” row, IPsec, GRE, L2TP, is technically significant. Unlike the other categories, this row does not list platforms such as Telegram or WhatsApp. What is being opened here are tunneling and network connectivity protocols. IPsec is used to create secure communications, authentication, confidentiality, integrity, and replay protection in network tunnels. L2TP is a Layer 2 tunneling protocol that does not provide full confidentiality on its own and is usually used together with IPsec. GRE is a Layer 3 tunneling protocol that can carry network traffic inside another tunnel, but it does not encrypt content itself and is usually paired with IPsec for security.
Opening these three protocols means that this category is likely designed for organizational connectivity, corporate VPNs, office to office links, access to foreign servers, cloud services, foreign APIs, payment systems, logistics, import and export operations, or private corporate networks, not simply to unblock a few social media platforms. This access allows the Islamic Republic to reduce the economic cost of disconnection for selected sectors during internet shutdowns or disruptions, without restoring the right to free access for the general public.
Ordinary Users: Reselling the Prewar Status Quo
The row for “ordinary users” should be seen as the core of the issue, not a secondary row. The phrase inside the table, “open protocol and restrictions on criminal content,” describes, technically and politically, almost exactly what the ordinary censorship model in Iran looked like before the wartime conditions. Access to the international internet was available as the default, but a set of domains, addresses, services, protocols, and content was filtered based on blocking lists and decisions by the Committee to Determine Instances of Criminal Content, the Filtering Committee.
Therefore, “Internet Pro for ordinary users” in the table is neither free internet nor special internet. It is the resale of the previous blacklist based censorship model: an internet in which general connectivity is available, but “criminal content” and targeted services remain restricted at the level of filtering and DPI.
The key difference is that after the war, the main access model for ordinary people shifted from a “blacklist” approach toward a “whitelist” approach. In the blacklist model, the internet is generally connected and the government blocks part of it. In the whitelist model, by contrast, the international internet as a service on the National Information Network is blocked or severely restricted, and only approved routes, websites, services, or user groups are allowed to pass.
This is the same situation that had been prepared for years in the logic of the National Information Network: a network designed to keep domestic services and controllable routes alive during disruptions or disconnection from the international internet. The document outlining the requirements of the National Information Network also identifies the Ministry of ICT as the executor of this network and emphasizes the need to define its requirements. In this framework, if “Internet Pro for ordinary users” is actually offered to ordinary users, it means that the Islamic Republic has turned a condition that was previously at least recognized as normal citizen access to the internet into a paid, authenticated, and privileged package.
The Security Dimensions of Internet Pro
This point is highly important for fact checking official claims. Officials and media outlets close to the state have usually explained wartime restrictions through the language of cyber security, wartime conditions, the need to protect the country, or crisis management. But when access resembling the prewar model is offered under the name “Internet Pro” and sold at roughly ten times the price for a one year package, the security argument faces a serious contradiction. If open protocols and a return to the previous filtering model pose an immediate security risk to the country, what makes selling that same model to an authenticated user technically secure?
The likely answer is that the issue is not only network security. It is attribution, control, and deterrence. The same behavior that is considered “dangerous” for an anonymous or less identified user becomes more tolerable for a user connected through a national ID number, mobile number, SIM card, and likely an authentication gateway, because the Islamic Republic’s security agencies can more easily trace, restrict, warn, disconnect, or prosecute that user.
Institutionally, this aligns precisely with the older project of the “valid identity system.” The Supreme Council of the Internet approved the valid identity system in 2019, defining the need for a valid identity for every technical, economic, cultural, social, political, and administrative interaction on the network. Article 3 of this resolution emphasizes that users’ interactions with the internet, the National Information Network, and domestic systems must pass through identity verification, and assigns the Ministry of ICT responsibility for verifying the identity of applicants and subscribers to fixed, mobile, and hosting communication services. More importantly, the explanation of the resolution’s effects says that anyone on the National Information Network or networks connected to it must be authenticated, and service providers must avoid accepting and passing through interactions that lack a valid identity. Therefore, Internet Pro should be understood not merely as a commercial package, but as an implementation stage in privileged, conditional, and identifiable connectivity.
Download file
The Economic Dimensions of Internet Pro
From the perspective of the political economy, this row also indicates real pressure on operators and the internet market. After the widespread outages, businesses told a representative of the Supreme National Security Council about the daily and even second by second losses caused by the internet shutdown. A committee including the National Center for the Internet and the Ministry of ICT was then tasked with designing a model for business internet access during outages.
Internet Pro sales began with MCI on February 25, and later Irancell and Rightel also received permission to provide similar services. This means that operators, whose revenue model depends on traffic consumption, package sales, and continued usage, have reached a point under the pressure of general internet restrictions where selling categorized versions of access has become attractive both for recovering revenue and for managing dissatisfaction among economic sectors. If “ordinary users” also enter this market, ordinary citizens themselves become customers buying back a right that has been taken from them.
Therefore, the noDPI1 2 row, or “ordinary users,” in the table is probably the most important conceptual evidence in this categorization. Unlike the academic, journalistic, or trade related rows, which show special access for privileged groups, this row shows that even the “normal” condition is no longer a public right. It is now a sellable tier in the market of tiered internet access.
The phrase “open protocol” probably means that, unlike the postwar whitelist based condition, the user has access to a wider set of protocols and internet routes. But the phrase “restrictions on criminal content” means that the Islamic Republic’s classic filtering by the Filtering Committee remains in place. Put simply, the Islamic Republic is selling the prewar internet, which was already heavily censored, as a product that is better than the current condition, but still controlled.
The likely answer lies in the mechanism of Internet Pro itself. This plan is not only about speed or stable connectivity. It is about turning internet access into an identifiable privilege. In this model, the user does not connect through a circumvention tool and an ambiguous identity, but through a national ID number, mobile number, SIM card, and an authentication path. This is the same logic that has been pursued for years in documents concerning the valid identity system and the National Information Network: every interaction on the network must be tied to a valid and attributable identity. For this reason, the ordinary users row shows that Internet Pro is not merely a crisis management tool or a mechanism for supporting businesses. It is a tool for normalizing a tiered, paid, and traceable internet in which even the minimum access to censored internet must be purchased again and activated with an official identity.
The image in the tweet above shows a commitment form. In other words, access is not offered as a normal user right, but as a privilege conditional on accepting responsibility, identity verification, and behavioral commitments. Its central phrase, “commitment form for accepting responsibility for the use of international internet,” is highly important narratively, because the title of the document itself turns the international internet into something for which the user must sign a commitment before use.
Images published on social media, including a sample commitment form for accepting responsibility for use of the international internet, an MCI text message activating Internet Pro, and photos of in person sales of the service at a booth attributed to MCI, show that this access model has not remained limited to the organizational level and has, at least in some cases, been offered as a consumer product.
The mechanism is clear: the user is authenticated through a phone number, national ID number, or similar pathways, accepts a commitment form, and then receives a level of internet access that is more open than the postwar whitelist based condition, while still remaining under the umbrella of filtering and individual responsibility. In this way, the international internet is transformed from a public right into a sellable, conditional, and attributable privilege.
The documents published from the Taknet commitment form, although not by themselves direct evidence of Internet Pro being sold to ordinary users, clarify the underlying legal logic of the same model: internet access in this framework is accompanied by identity verification, logging, data retention, and the transfer of responsibility to the subscriber. This means that if an organization, company, workplace, or public WiFi provider wants to distribute internet access within its own environment, responsibility for identifying and recording the behavior of end users is transferred from the operator to the legal subscriber. This is exactly the model of “distributed surveillance”: the state or operator does not necessarily authenticate the final user directly at every point. Instead, the chain of responsibility is transferred to the company, organization, workplace, hotel, shopping center, or WiFi provider. As a result, the legal subscriber also becomes an enforcement node for identity verification and data logging.
Conclusion
After the war between the United States and Israel and Iran, the Islamic Republic implemented “Internet Pro” as a new version of tiered internet access in response to social and economic pressure caused by internet shutdowns and restrictions. Evidence such as the access tier table, contradictory reactions from officials, package sales by operators, commitment forms, and activation samples shows that internet access is no longer defined on the basis of equal user rights. Instead, it is distributed according to professional class, institutional affiliation, identity verification, and the level of security trust.
This model has moved beyond special access for academics, journalists, and traders. Now even “ordinary users” must pay to return to a version of the censored prewar internet and enter the network with an attributable identity. The core argument is that Internet Pro is not a tool for reopening the internet. It is a mechanism for normalizing whitelist internet, reselling censored internet, and expanding distributed surveillance over users.